Massive AitM Campaign Bypasses 2FA
- Ben Card

- Aug 8, 2022
- 3 min read
A brand new, global-scale phishing campaign is currently active and is using adversary-in-the-middle (AitM) techniques to bypass security protections and thereby compromise email accounts across a range of targeted organizations.

“It uses an adversary-in-the-middle (AitM) attack technique capable of bypassing multi-factor authentication,” Sudeep Singh and Jagadeeswar Ramanukolanu, Zscaler researchers, explained. “The campaign is specifically designed to reach end users in enterprises that use Microsoft’s email services.”
Primary targets include insurance, energy, manufacturing, fintech, lending, and federal credit union entities located in the U.S., New Zealand, U.K., and Australia.
This severity of phishing campaign is unfortunately not entirely unheard of. Microsoft disclosed last month that the number of organizations that had been targeted since September 2021 by means of AitM techniques totaled more than 10,000, according to their research. The technique has been effectively used by attackers to breach accounts secured with two-factor authentication (2FA)/multi-factor authentication (MFA).
It is estimated that the current campaign has been active since June 2022, and it typically starts with an invoice-related email that includes an HTML attachment, which itself includes an embedded phishing URL.
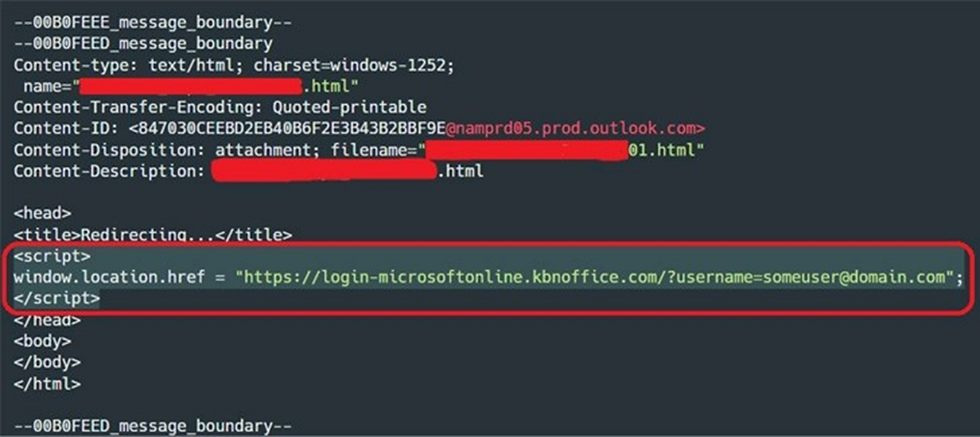
If the attachment is opened it rapidly fingerprints the compromised machine to determine whether the victim is actually the intended target or member of the target organization. Once the target has been verified, the code in the attachment uses a web browser to redirect the victim to a webpage that appears to be a login page for Microsoft Office.

The use of a number of different attack components in the way the creators of this campaign do is what makes it so unique. A key component is the use of open redirect pages hosted by Google Ads and Snapchat to load the malicious web page, rather than embedding malicious URLs directly in the email itself.

As mentioned above, AitM phishing attacks are capable of much more than the traditional phishing approaches when it comes to stealing credentials; this is particularly true when dealing with authentication using MFA--a security measure that is meant to prevent authentication even if someone knows a username and password.
The way that the attackers circumvent MFA is via code in the malicious web page, whereby a proxy is instantiated that captures and the forwards all communication between the client (i.e., the victim’s machine) and the email server. The proxy functionality is one part of an overall attack “kit.”
The researchers stated that "the kits intercept the HTML content received from the Microsoft servers, and before relaying it back to the victim, the content is manipulated by the kit in various ways as needed, to make sure the phishing process works”.
The kit also replaces all links to Microsoft domains with equivalent links to the phishing domain to ensure that the communications remain intact throughout the duration of the time the fraudulent website is acting as proxy.
Security researchers from Zscaler went on to say they observed the attackers manually logging into a compromised account eight minutes following credential theft; the malicious actors then read emails and checked the victim's profile information.
Additionally, in some instances, the attackers used compromised email accounts to send additional phishing emails as part of the same campaign, conducting business email compromise (BEC) attacks—increasing their effectiveness.

"Even though security features such as multi-factor authentication (MFA) add an extra layer of security, they should not be considered as a silver bullet to protect against phishing attacks," explained the research team. "With the use of advanced phishing kits (AiTM) and clever evasion techniques, threat actors can bypass both traditional as well as advanced security solutions."
To learn more about phishing, or to make sure your system is secure. Contact Webcheck Security.




Comments